The Cloud’s Silver Lining Has a Dark Side: Top 5 Cloud Security Threats and How to Mitigate Them
Cloud computing adoption has skyrocketed thanks to its flexibility, scalability, and cost-savings. However, recent high-profile breaches illustrate the vital need for cloud security. In 2022 alone, over 25 billion records were stolen or exposed in the cloud according to Risk Based Security. As your company moves to the cloud, be sure to prioritize security.
This post examines the top cloud threats and provides actionable tips to help you develop a layered defense.
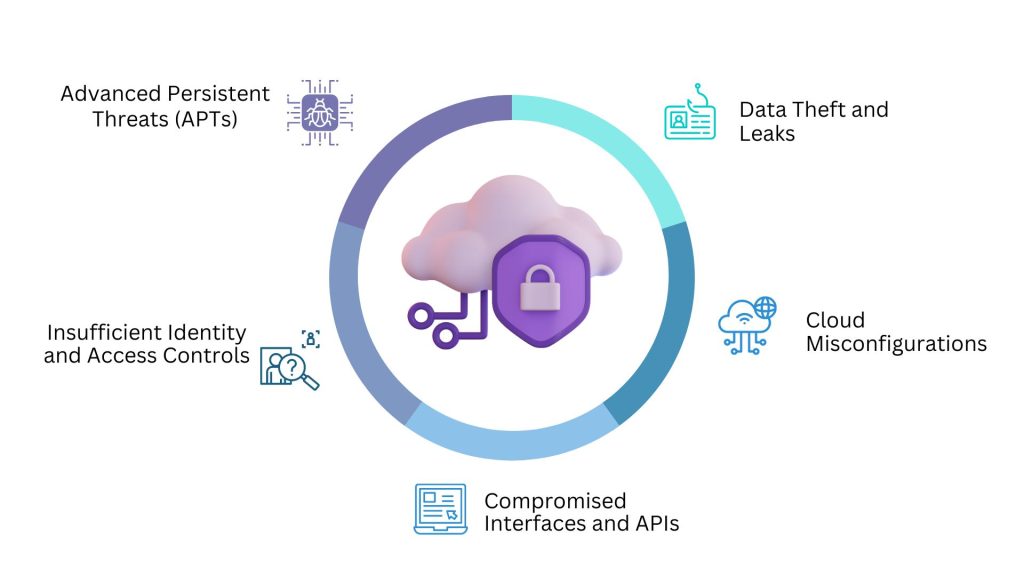
1. Data Theft and Leaks
Data breaches remain the number one cloud security threat. Sensitive customer data, financial records, credentials, and intellectual property are prime targets for hackers. For example, in 2022 Uber suffered a data breach exposing info on over 57 million riders and drivers.
- Leverage tools like encryption, tokenization, and data loss prevention to secure critical data.
- Implement multi-factor authentication (MFA) to prevent stolen credentials-related breaches.
- Follow the principle of least privilege access across your cloud environment.
2. Cloud Misconfigurations
Misconfigured cloud resources are the top cause of data exposures according to Gartner. Basic slip-ups like leaving storage buckets public, failing to restrict permissions, and disabling encryption can jeopardize your data.
- Use cloud-native and third-party tools to automatically scan for misconfigured resources. AWS Config and Azure Security Center are good options.
- Enforce configuration management processes and compliance monitoring to prevent human error. Chef, Puppet, and Salt Stack are leading solutions.
- Educate your teams on proper cloud security settings for the specific services you utilize.
3. Compromised Interfaces and APIs
APIs and interfaces enable critical management and functionality. But they also create vulnerabilities if not properly secured. For example, both Facebook and Equifax suffered major breaches in part due to unprotected APIs.
- Harden APIs with protocols like OAuth 2.0 and mutual TLS authentication. Use API gateways to manage traffic and security policies.
- Perform regular static and dynamic analysis security testing on APIs and interfaces. Burp Suite and OWASP ZAP are useful tools.
- Monitor API traffic for abnormal behavior that could signal an attack.
4. Insufficient Identity and Access Controls
Without vigorous access and identity management, unauthorized users and threats can easily infiltrate your environment. Compromised credentials were linked to over 20% of breaches last year according to Verizon.
- Institute robust identity provider (IdP) solutions like Okta, Azure AD, or ForgeRock for provisioning, authentication, and access visibility.
- Conduct periodic entitlement reviews to prune unnecessary permissions and overprovisioned access.
- Implement processes to promptly revoke access when employees leave or change roles.
5. Advanced Persistent Threats (APTs)
APTs are stealthy, prolonged attacks that can quietly lurk in your cloud environment for months or longer. Skilled adversaries like state-sponsored hackers often orchestrate them. For instance, security researchers recently uncovered a massive APT campaign dubbed Cloud Snooper.
- Leverage threat intelligence from providers like CrowdStrike and Darktrace to stay on top of new vulnerabilities, exploits, and hacker tactics.
- Deploy tools with behavioral analytics and machine learning to quickly recognize subtle anomalies that could indicate an APT.
- Develop and practice an incident response plan to contain and remediate APTs swiftly.
While the cloud revolutionizes business capabilities, it also transforms risk. Following security best practices and taking a proactive stance are imperative. Regularly assess your cloud vulnerabilities, implement robust controls tailored to your architecture, and ensure your team has cloud security expertise. With vigilance and preparation, you can confidently unlock the cloud’s potential while keeping data secure.

